AWS port
forwarding,
without friction.
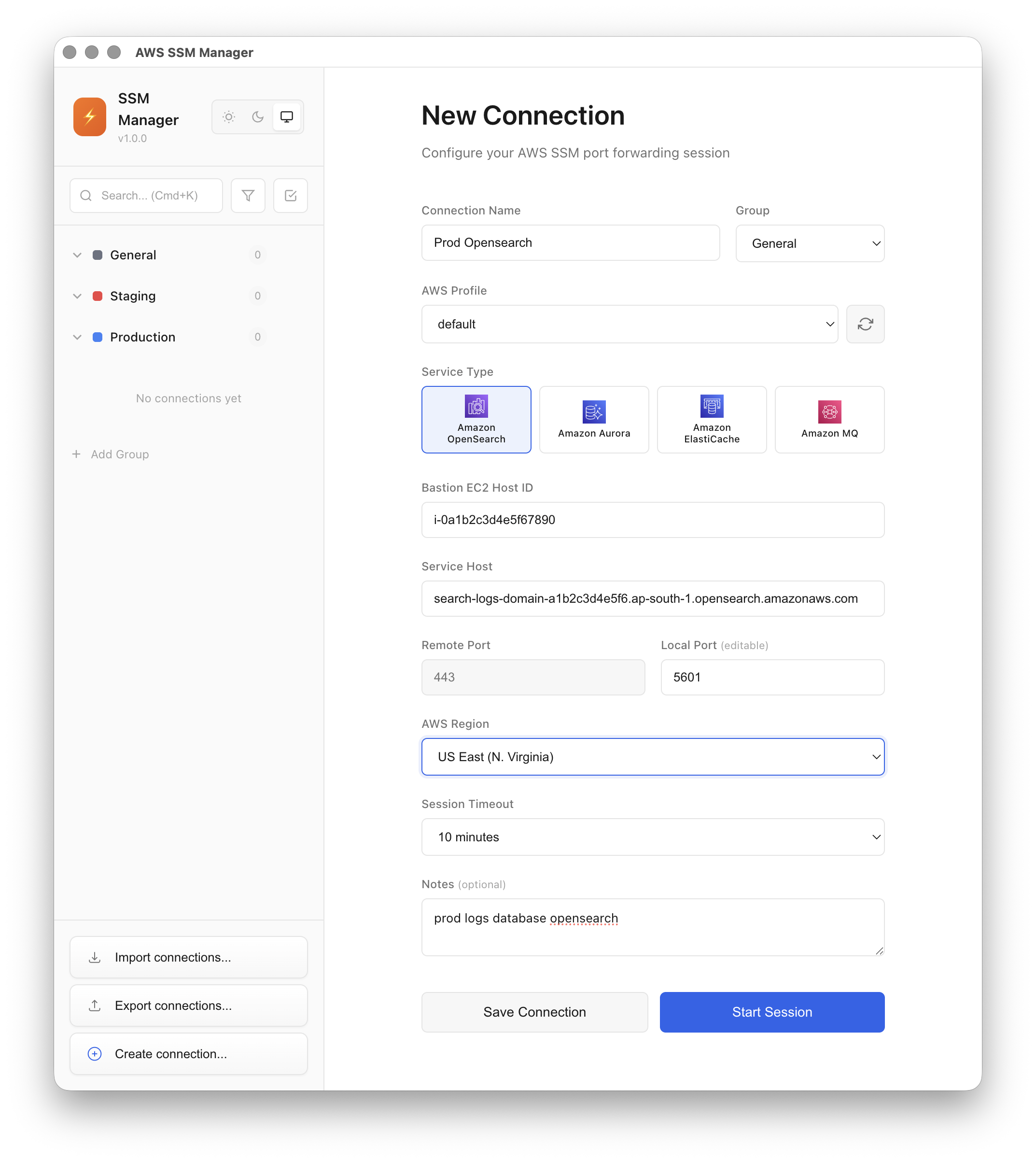
Save SSM connections once, launch them in one click. No open ports, no SSH keys, no bastion hosts — just IAM, with a UI that doesn't slow you down.